- Topic1/3
7k Popularity
27k Popularity
10k Popularity
5k Popularity
173k Popularity
- Pin
- Hey fam—did you join yesterday’s [Show Your Alpha Points] event? Still not sure how to post your screenshot? No worries, here’s a super easy guide to help you win your share of the $200 mystery box prize!
📸 posting guide:
1️⃣ Open app and tap your [Avatar] on the homepage
2️⃣ Go to [Alpha Points] in the sidebar
3️⃣ You’ll see your latest points and airdrop status on this page!
👇 Step-by-step images attached—save it for later so you can post anytime!
🎁 Post your screenshot now with #ShowMyAlphaPoints# for a chance to win a share of $200 in prizes!
⚡ Airdrop reminder: Gate Alpha ES airdrop is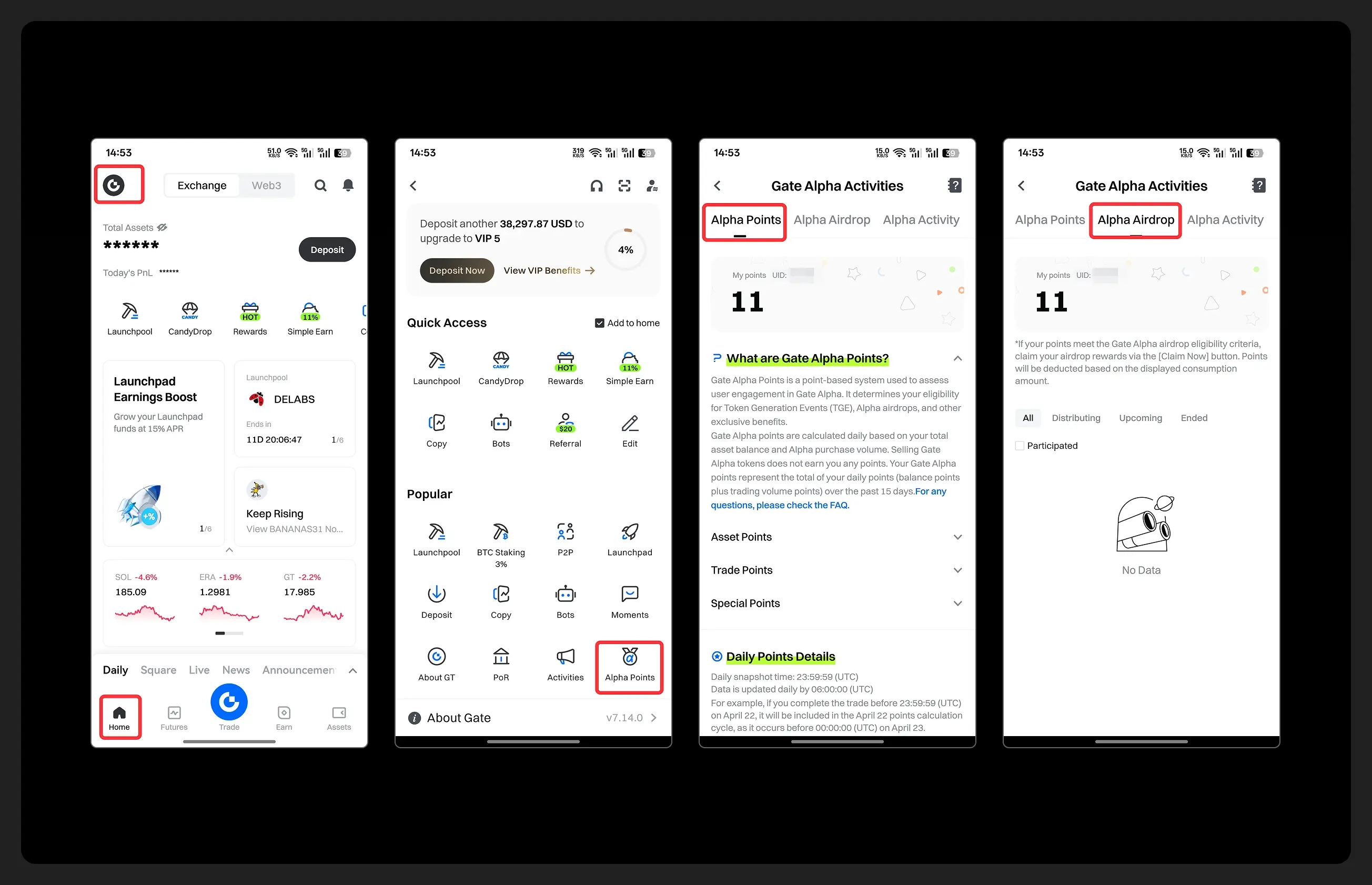
- Gate Futures Trading Incentive Program is Live! Zero Barries to Share 50,000 ERA
Start trading and earn rewards — the more you trade, the more you earn!
New users enjoy a 20% bonus!
Join now:https://www.gate.com/campaigns/1692?pid=X&ch=NGhnNGTf
Event details: https://www.gate.com/announcements/article/46429
- Hey Square fam! How many Alpha points have you racked up lately?
Did you get your airdrop? We’ve also got extra perks for you on Gate Square!
🎁 Show off your Alpha points gains, and you’ll get a shot at a $200U Mystery Box reward!
🥇 1 user with the highest points screenshot → $100U Mystery Box
✨ Top 5 sharers with quality posts → $20U Mystery Box each
📍【How to Join】
1️⃣ Make a post with the hashtag #ShowMyAlphaPoints#
2️⃣ Share a screenshot of your Alpha points, plus a one-liner: “I earned ____ with Gate Alpha. So worth it!”
👉 Bonus: Share your tips for earning points, redemption experienc
- 🎉 The #CandyDrop Futures Challenge is live — join now to share a 6 BTC prize pool!
📢 Post your futures trading experience on Gate Square with the event hashtag — $25 × 20 rewards are waiting!
🎁 $500 in futures trial vouchers up for grabs — 20 standout posts will win!
📅 Event Period: August 1, 2025, 15:00 – August 15, 2025, 19:00 (UTC+8)
👉 Event Link: https://www.gate.com/candy-drop/detail/BTC-98
Dare to trade. Dare to win.
Binius protocol: Breakthrough optimization of STARKs on binary domains
Analysis of Binius STARKs Principles and Optimization Thoughts
1 Introduction
One of the main reasons for the inefficiency of STARKs is that most numerical values in actual programs are relatively small, such as indices in for loops, boolean values, counters, etc. However, to ensure the security of proofs based on Merkle trees, when using Reed-Solomon coding to expand the data, many additional redundant values will occupy the entire field, even though the original values themselves are very small. To address this issue, reducing the size of the field has become a key strategy.
The bit width of the 1st generation STARKs encoding is 252 bits, the bit width of the 2nd generation STARKs encoding is 64 bits, and the bit width of the 3rd generation STARKs encoding is 32 bits. However, the 32-bit encoding still has a lot of wasted space. In comparison, the binary field allows for direct bit manipulation, making the encoding compact and efficient without any wasted space, which is the 4th generation STARKs.
Compared to recent discoveries of finite fields such as Goldilocks, BabyBear, and Mersenne31, research on binary fields can be traced back to the 1980s. Currently, binary fields are widely used in cryptography, with typical examples including:
Advanced Encryption Standard ( AES ), based on the F28 field;
Galois Message Authentication Code ( GMAC ), based on the F2128 field;
QR code, using Reed-Solomon coding based on F28;
The original FRI and zk-STARK protocols, as well as the Grøstl hash function which entered the SHA-3 finals, are based on the F28 field and are a very suitable recursive hash algorithm.
When using smaller fields, the extension field operation becomes increasingly important for ensuring security. The binary field used by Binius relies entirely on extension fields to guarantee its security and practical usability. Most of the polynomials involved in Prover computations do not need to enter the extension field and can operate under the base field, achieving high efficiency in small fields. However, random point checks and FRI calculations still need to delve into larger extension fields to ensure the required level of security.
When constructing proof systems based on binary fields, there are two practical issues: the size of the field used when calculating the trace representation in STARKs should be greater than the degree of the polynomial; when committing to a Merkle tree in STARKs, Reed-Solomon encoding must be performed, and the size of the field used should be greater than the size after encoding expansion.
Binius proposed an innovative solution that addresses both issues separately and achieves this by representing the same data in two different ways: first, by using multivariable ( specifically as multilinear ) polynomials instead of univariate polynomials, representing the entire computational trajectory through its values on "hypercubes" (; secondly, since the length of each dimension of the hypercube is 2, it cannot perform standard Reed-Solomon expansion like STARKs, but the hypercube can be viewed as a square ), and based on that square, Reed-Solomon expansion can be performed. This method greatly enhances coding efficiency and computational performance while ensuring security.
2 Principle Analysis
The construction of most current SNARKs systems typically includes the following two parts:
Information-Theoretic Polynomial Interactive Oracle Proof, PIOP(: PIOP serves as the core of the proof system, transforming the input computational relationship into verifiable polynomial equations. Different PIOP protocols allow the prover to send polynomials progressively through interaction with the verifier, enabling the verifier to validate the correctness of the computation by querying the evaluation results of a small number of polynomials. Existing PIOP protocols include: PLONK PIOP, Spartan PIOP, and HyperPlonk PIOP, each of which has a different approach to handling polynomial expressions, thereby affecting the performance and efficiency of the entire SNARK system.
Polynomial Commitment Scheme ): The Polynomial Commitment Scheme is used to prove whether the polynomial equations generated by PIOP hold true. PCS is a cryptographic tool that allows the prover to commit to a certain polynomial and later verify the evaluation results of that polynomial while hiding other information about the polynomial. Common polynomial commitment schemes include KZG, Bulletproofs, FRI ( Fast Reed-Solomon IOPP ), and Brakedown, among others. Different PCS have different performance, security, and applicable scenarios.
According to specific requirements, different PIOPs and PCSs can be selected, and combined with suitable finite fields or elliptic curves, it is possible to construct proof systems with different attributes. For example:
• Halo2: Combined from PLONK PIOP and Bulletproofs PCS, based on the Pasta curve. Halo2 is designed with a focus on scalability and the removal of the trusted setup in the ZCash protocol.
• Plonky2: Combines PLONK PIOP and FRI PCS, based on the Goldilocks field. Plonky2 is designed for efficient recursion. When designing these systems, the chosen PIOP and PCS must match the finite field or elliptic curve used to ensure the system's correctness, performance, and security. The choice of these combinations not only affects the proof size and verification efficiency of SNARKs but also determines whether the system can achieve transparency without a trusted setup, and whether it can support extended features such as recursive proofs or aggregated proofs.
Binius: HyperPlonk PIOP + Brakedown PCS + binary fields. Specifically, Binius includes five key technologies to achieve its efficiency and security. First, the arithmetic based on the tower of binary fields ( towers of binary fields ) forms the foundation of its computation, enabling simplified operations within binary fields. Second, Binius adapts HyperPlonk product and permutation checks in its interactive Oracle proof protocol ( PIOP ), ensuring secure and efficient consistency checks between variables and their permutations. Third, the protocol introduces a new multilinear shift proof, optimizing the efficiency of verifying multilinear relationships over small fields. Fourth, Binius employs an improved Lasso search proof, providing flexibility and strong security for the search mechanism. Finally, the protocol uses a small field polynomial commitment scheme ( Small-Field PCS ), enabling an efficient proof system over binary fields and reducing the overhead typically associated with large fields.
( 2.1 Finite Fields: Arithmetic Based on Towers of Binary Fields
Towered binary fields are key to achieving fast verifiable computation, primarily due to two aspects: efficient computation and efficient arithmetic. Binary fields inherently support highly efficient arithmetic operations, making them an ideal choice for performance-sensitive cryptographic applications. Furthermore, the structure of binary fields supports a simplified arithmetic process, meaning that operations performed over binary fields can be represented in a compact and easily verifiable algebraic form. These features, combined with the ability to fully leverage its hierarchical characteristics through tower structures, make binary fields particularly suitable for scalable proof systems such as Binius.
The term "canonical" refers to the unique and direct representation of elements in the binary field. For example, in the simplest binary field F2, any k-bit string can be directly mapped to a k-bit binary field element. This is different from prime fields, which cannot provide such a canonical representation within a given bit length. Although a 32-bit prime field can be contained within 32 bits, not every 32-bit string can uniquely correspond to a field element, whereas the binary field has the convenience of this one-to-one mapping. In the prime field Fp, common reduction methods include Barrett reduction, Montgomery reduction, as well as special reduction methods for specific finite fields like Mersenne-31 or Goldilocks-64. In the binary field F2k, commonly used reduction methods include special reduction ) as used in AES, Montgomery reduction ( as used in POLYVAL, and recursive reduction ) as used in Tower ###. The paper "Exploring the Design Space of Prime Field vs. Binary Field ECC-Hardware Implementations" points out that in binary fields, both addition and multiplication operations do not require carry, and the squaring operation in binary fields is very efficient because it follows the simplification rule of (X + Y )2 = X2 + Y 2.
As shown in Figure 1, a 128-bit string: This string can be interpreted in various ways in the context of binary fields. It can be viewed as a unique element in a 128-bit binary field, or parsed as two 64-bit tower field elements, four 32-bit tower field elements, 16 8-bit tower field elements, or 128 F2 field elements. This flexibility of representation does not require any computational overhead, just a typecast of the bit string (typecast), which is a very interesting and useful property. At the same time, small field elements can be packed into larger field elements without additional computational overhead. The Binius protocol takes advantage of this feature to enhance computational efficiency. Additionally, the paper "On Efficient Inversion in Tower Fields of Characteristic Two" discusses the computational complexity of multiplication, squaring, and inversion operations in an n-bit tower binary field ( decomposed into m-bit subfields ).
( 2.2 PIOP: Adapted HyperPlonk Product and Permutation Check ------ Applicable to binary fields
The PIOP design in the Binius protocol draws on HyperPlonk and employs a series of core checking mechanisms to verify the correctness of polynomials and multivariate sets. These core checks include:
GateCheck: Verify whether the confidential witness ω and public input x satisfy the circuit operation relation C)x, ω(=0, to ensure the correct operation of the circuit.
PermutationCheck: Verify whether the evaluation results of two multivariate polynomials f and g on the Boolean hypercube are a permutation relation f)x( = f)π###x(), to ensure the consistency of the arrangement among the polynomial variables.
LookupCheck: Verify whether the evaluation of the polynomial is within the given lookup table, that is, f(Bµ) ⊆ T(Bµ(, ensuring that certain values are within the specified range.
MultisetCheck: Check whether two multivariable sets are equal, that is, {)x1,i,x2,)}i∈H={(y1,i,y2,)}i∈H, ensuring consistency among multiple sets.
ProductCheck: Check whether the evaluation of the rational polynomial on the Boolean hypercube is equal to a declared value ∏x∈Hµ f(x) = s, to ensure the correctness of the polynomial product.
ZeroCheck: Verify whether a multivariate polynomial is zero at any point on the Boolean hypercube ∏x∈Hµ f(x) = 0, ∀x ∈ Bµ, to ensure the distribution of the polynomial's zeros.
SumCheck: A method to verify whether the sum of a multivariate polynomial is equal to the declared value ∑x∈Hµ f(x) = s. By transforming the evaluation of a multivariate polynomial into a univariate polynomial evaluation, it reduces the computational complexity for the verifier. Additionally, SumCheck allows for batching by introducing randomness to construct linear combinations for batch verification of multiple sum-check instances.
BatchCheck: Based on SumCheck, verifies the correctness of multiple multivariate polynomial evaluations to improve protocol efficiency.
Although Binius and HyperPlonk have many similarities in protocol design, Binius has made improvements in the following three areas:
ProductCheck Optimization: In HyperPlonk, ProductCheck requires that the denominator U is non-zero everywhere on the hypercube, and the product must equal a specific value; Binius simplifies this check process by specializing that value to 1, thereby reducing computational complexity.
Handling of division by zero issue: HyperPlonk fails to adequately handle division by zero situations, resulting in an inability to assert the non-zero issue of U on the hypercube; Binius correctly addresses this problem, allowing Binius's ProductCheck to continue processing even when the denominator is zero, enabling generalization to any product value.
Cross-column PermutationCheck: HyperPlonk does not have this feature; Binius supports PermutationCheck across multiple columns, allowing Binius to handle more complex polynomial arrangement scenarios.
Therefore, Binius has improved the existing PIOPSumCheck mechanism, enhancing the flexibility and efficiency of the protocol, especially in handling more complex multivariable polynomial verification, providing stronger functional support. These improvements not only address the limitations in HyperPlonk but also lay the foundation for future proof systems based on binary fields.
( 2.3 PIOP: New multilinear shift argument------Applicable to boolean hypercube
In the Binius protocol, the construction and processing of virtual polynomials is one of the key technologies, capable of effectively generating and manipulating polynomials derived from input handles or other virtual polynomials. Here are two key methods: